Researchers from the University of Stuttgart and the University of Munich Ludwig-Maximilian created a technique for “thermal attacks”. In this work, they examined the effect of the PIN / Pattern property on its vulnerability to thermal attacks.
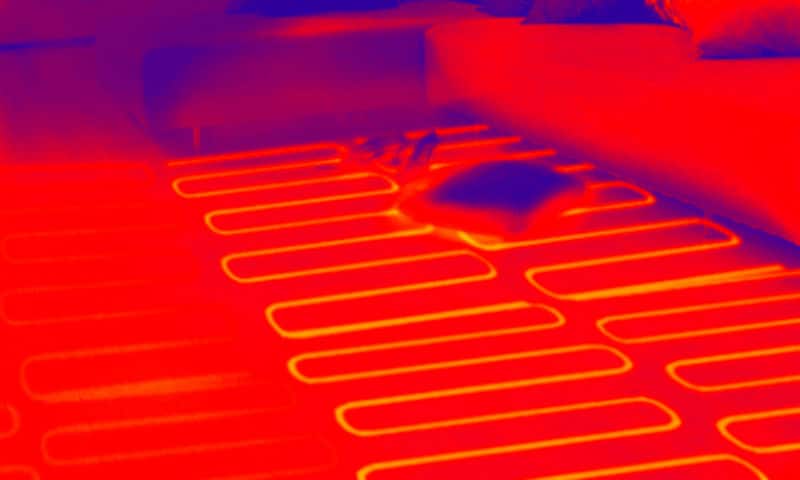
The fact is that after typing a PIN or a graphic password on the screen of the mobile device, there remains a heat trace from the user’s hands, which will be clearly discernible for about 30 seconds after dialing. The modern thermal imager (the researchers used a thermal imager with a sensitivity of 0.04 degrees Celsius), is able to “extract” these data (PIN). But despite this, researchers write that to protect themselves from “thermal attacks” is possible, for this it is enough to hold your hand across the screen of the device.
The report (PDF) for this study will be officially presented at the ACM CHI 2017 conference in March 2017.