What to do after hack – 5 unusual places where you can find evidence
This article describes how and where to find evidence of tampering. It shows the 5 places that you want to see in the first place during the investigation.
The author shows places of interest in Microsoft Windows, which can be viewed on to find out, for example, post-login information, information about which software is running, information about which were open files, information from NTFS journal, and also several other places of interest, which may mean that something will go wrong.
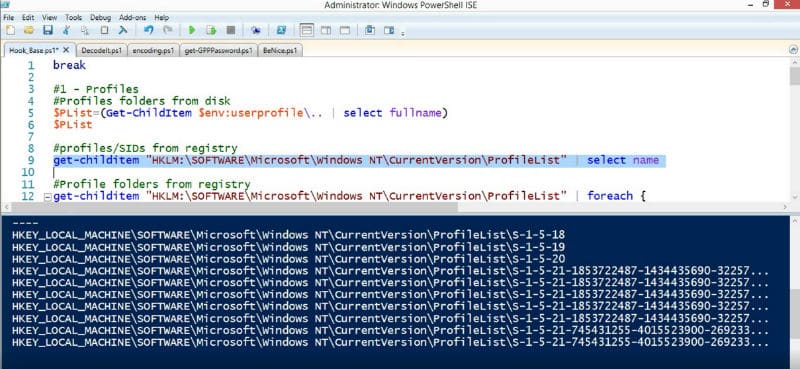
The first of what will be discussed is the list of profiles. It is a place where we can find some very interesting data on the profiles of history. Of course, someone can be intelligent and to remove the data from the registry completely, but it is something that is worth checking out.
Second place – Prefetch. For the analysis tool used: CQPrefetchParser. CQPrefetchParser accepts a prefetch parameter file for analysis. CQPreferchParser shows us very nicely all the interesting paths that were related with that particular prefetch file. It also shows modules, the different types of DLLs that were loaded when this particular executable was running.
The third tool called CARD Cache. It’s a very simple tool. You can download the client cache Terminal Server that is located in each profile.
The following is called Automatic Destinations. Automatic destinations contain the history of all the interesting files that were ever used, for example, text files, that we were opened by Notepad.
The fifth place is associated with the file system NTFS Journal, or USN journal, which contains the entire history of file changes.
You can read a more detailed description of each place here or download utilities.




Comments are closed.