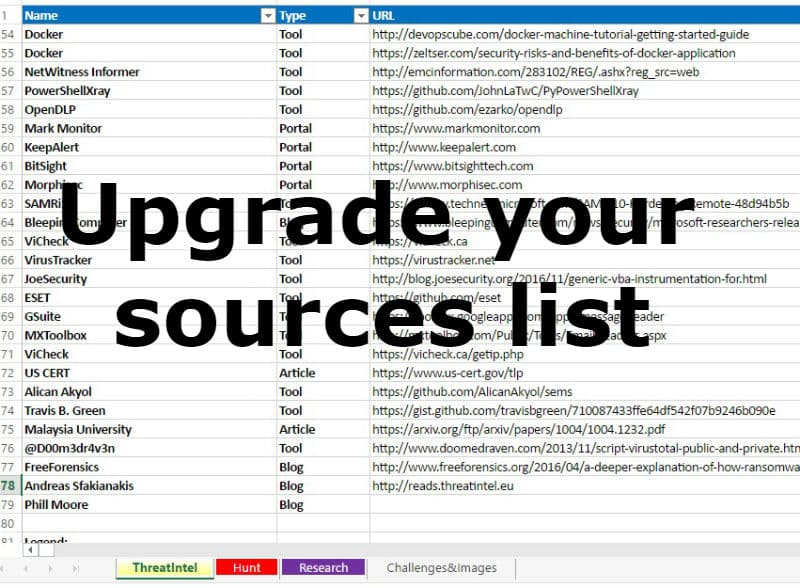
Mary Ellen created her sources list. She updated her Follow Links spreadsheet and added Threat Intelligence links. In top she shared her final spreadsheet with info about Threat Intelligence portals, Hunt tactics and more malware links.
The document contains four tabs. Such us: ‘ThreatIntel’, ‘Hunt’, ‘Research’, ‘Challenges&Images’. So, you don’t miss important sources. A lot of the entries are free or open source.
It is great work. You can find the document here.