Extracting data from passcode-locked devices is always challenging, especially when we are talking about iOS devices.
Today we are going to tell you about one of the ways of how a digital forensics examiner can extract data from a passcode-locked iOS device – iPhone or iPad, and get case related information.
If you are an iOS device owner, you’ve connected your smartphone or tablet to your PC or Mac, at least once, for example, for managing music.
When you connect your iDevice to your computer, iTunes automatically creates lockdown files for it. These particular files will help an examiner to extract data from the mobile device without knowing the passcode.
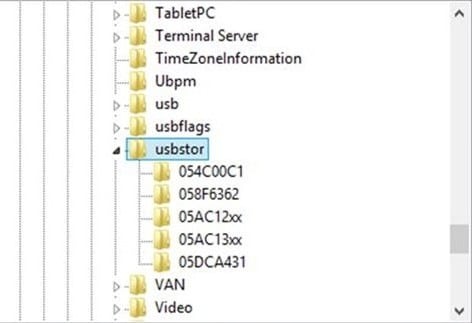
Here are the locations for these files:
Mac OS X – \private\var\db\lockdown;
Windows 2000 and XP – C:\Documents and Settings\All Users\Application Data\Apple\Lockdown;
Windows Vista, 7, 8 and 10 – C:\ProgramData\Apple\Lockdown.

For successful data extraction, a digital forensics examiner must put these files from suspects computer to his workstation (to the same folder). After that the data can be extracted via your favourite imaging tool.
It’s important to note, that if the iDevice being examined running iOS version 9 or later and was rebooted after it was locked, you can’t use this approach.





Comments are closed.