The most popular Instant Messengers are Telegram, WhatsApp, Viber. These instant messengers have both mobile applications and desktop applications. Today we will look at the types of data an examiner can detect when researching desktop applications of Telegram, WhatsApp, Viber.
Telegram
Telegram is a cloud-based applications. All chats are in the cloud. In part, chats can be found on mobile devices.
Telegram files (desktop Application) can be found by the way (Windows 8/10): / Users /% User profile% / AppData / Roaming / Telegram / Telegram Desktop

Telegram subfolders
In this folder are:
Executable file – Telegram.exe
Log file – log.txt
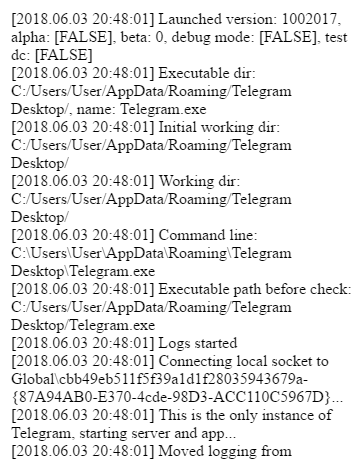
Fragment of the log.txt file
The subfolder D877F783D5D3EF8C contains files.
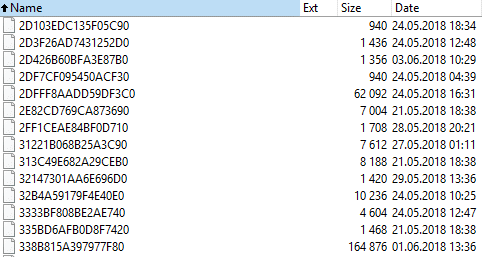
Files in the subfolder D877F783D5D3EF8C
Probably, these files are temporary files of the Telegram desktop Application. Identify their contents failed. These files are probably encrypted.
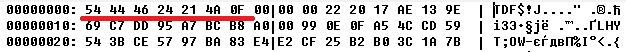
All these files have the header 54 44 46 24 21 4A 0F.
WhatsApp stores chats on members. New chat messages are stored in the WhatsApp cloud and can be retrieved from there.
The WhatsApp (desktop Application) files can be found on the path (Windows 8/10): / Users /% User profile% / AppData / Roaming / WhatsApp

WhatsApp subfolders
NOTE: The log file of WhatsApp installation is located on the path / Users /% User profile% / AppData / Local / WhatsApp and has the name SquirrelSetup.log
The subfolder databases contains on a SQLite file – Databases.db. But this file does not contain contacts or chats.
Other subfolders contain temporary files of the WhatsApp desktop Application.
The most interesting is the subfolder Cache.
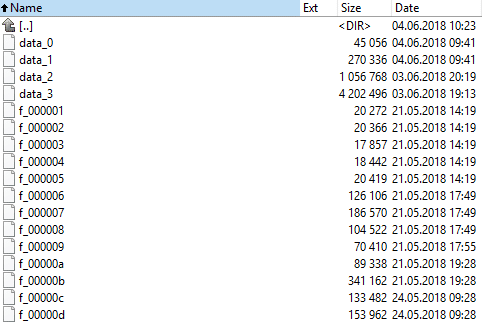
Files in the subfolder Cache
The file data_2 contains avatars of the members.
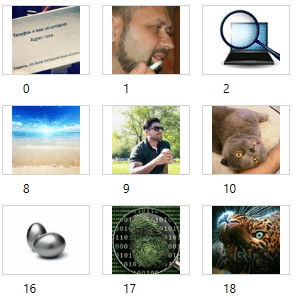
Avatars
and links to the members’ accounts (including phone numbers of the members)
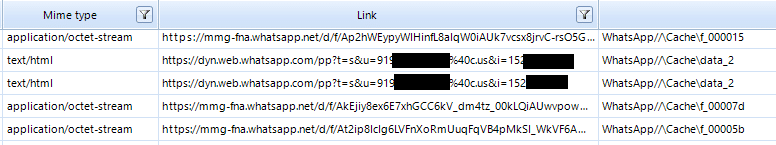
The remaining files in the Cache subfolder can be images, videos, documents, which members exchange in chats. Probably, these files are encrypted. As a rule, in these files, in addition to the encrypted content, you can find the same links:
Viber
Viber stores chats on devices members. New chat messages are stored in the Viber cloud and can be retrieved from there.
You can find the Viber files (desktop Application) by the path (Windows 8/10): / Users /% User profile% / AppData / Roaming / ViberPC /
Where the name of one of the subfolder is the phone number of the owner of this Viber account.
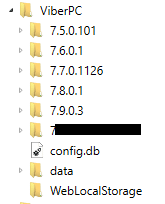
In folder ViberPC there is a file config.db which contains tables
Accounts:
![]()
CommonSettings:

In the subfolder with a name that is the same as the phone number of the owner of the Viber account, there are:
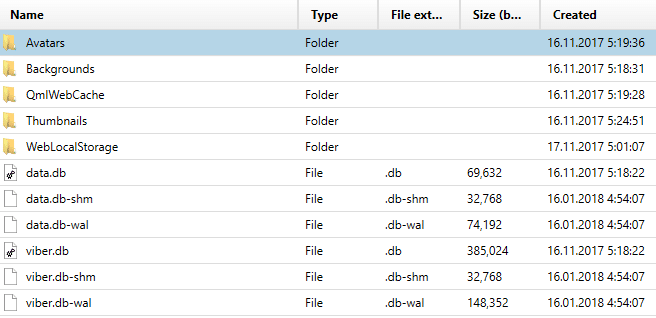
The file data.db.
Probably the file contains the auxiliary data necessary for the correct operation of this Instant Messenger.
The viber.db file, which contains Viber Calls, Viber Chat Messages, Viber Contacts (this information can be extracted with AXIOM (Magnet Forensics) or Belkasoft Evidence Center (Belkasoft) .When examining the viber.db file with SQLite Viewer, from the following additional information can be extracted:
– additional information about the settings of the ViberPC program;
– information about downloaded and uploaded files;
-chat info;
-recovered chats;
-version of the Instant Messenger;
-etc.

The data types extracted from the viber.db file with AXIOM
In the subfolder Avatars are avatars of Viber’s members.
In the subfolder Backgrounds are background images.
The Thumbnails subfolder contains thumbnails of images that were downloaded and uploaded by Viber’s members.
Conclusion
Instant Messengers Developers declare that chats are partially or completely stored on devices members. However, this statement is not true for Telegram Desktop Application and WhatsApp Desktop Application. An examiner is unable to remove chats, or decrypt the encrypted temporary files of the applications.
When analyzing the WhatsApp Desktop Application, an examiner can extract avatars and phone numbers from the WhatsApp’s members.
When analyzing Viber Desktop Application an examiner can extract Viber Calls, Viber Chat Messages, Viber Contacts, avatars and media cache. With deep analysis of viber.db with a SQLite Viewer tool, additional information can be extracted.
Happy forensicating!
About the authors
Oleg Skulkin, GCFA, MCFE, ACE, is a DFIR enthusional (enthusiast + professional), Windows Forensics Cookbook and Practical Mobile Forensics co-author.
Igor Mikhaylov, MCFE, EnCE, ACE, OSFCE, is a digital forensic examiner with more than 20 years of experience and Mobile Forensics Cookbook author.